Introduction
When connecting to SFTP servers in SSIS, some servers may require specific cipher or encryption algorithms for secure communication. The ZappySys Secure FTP Task supports advanced encryption configurations, allowing you to customize key exchange methods, MAC algorithms, encryption ciphers, and host key validation techniques.
In this tutorial, you’ll learn how to configure SFTP cipher algorithms in the ZappySys Secure FTP connection manager to meet your security or compatibility requirements.
Prerequisites
- Download and install the ZappySys SSIS PowerPack.
Steps
Step 1: Open the Secure FTP Connection Manager
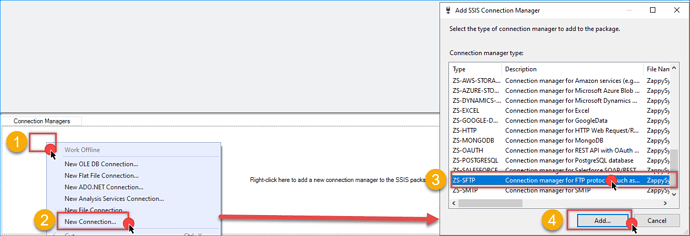
- Open your SSIS project in Visual Studio (SSDT).
- Go to the Connection Managers panel at the bottom.
- Select an existing ZS-SFTP connection or right-click to create a New Connection using the ZappySys Secure FTP provider.
Step 2: Access the Encryption Settings
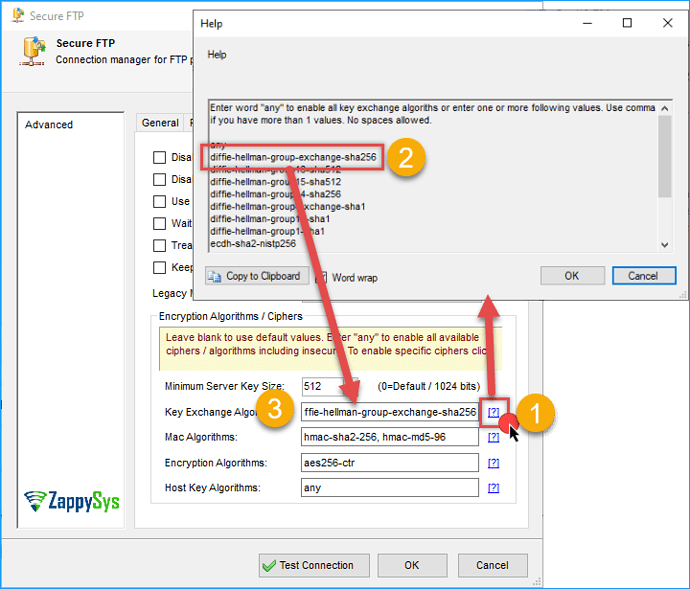
- In the Secure FTP Connection Manager, go to the Advanced tab.
- Locate the section labeled Encryption Algorithms / Ciphers. This section allows you to customize the encryption handshake with the server.
Step 3: Configure Cipher Algorithm Settings
Here’s a breakdown of each configurable setting:
-
Key Exchange Algorithms: Defines the method for securely exchanging cryptographic keys with the server. Examples:
diffie-hellman-group14-sha1, ecdh-sha2-nistp256, diffie-hellman-group-exchange-sha256 -
MAC Algorithms: Specifies the Message Authentication Code algorithms used for data integrity checks. Examples:
hmac-sha2-256, hmac-sha1 -
Encryption Algorithms: Determines which encryption ciphers are used for data transmission. Examples:
aes128-ctr, aes256-ctr, 3des-cbc -
Host Key Algorithms: Sets the method for verifying the server’s host key. Examples:
ssh-rsa, rsa-sha2-256 -
To enable all supported algorithms, enter:
any.
You can enter multiple algorithms by separating them with commas without spaces.
Step 4: Test the Connection
After configuring the algorithms:
- Click the Test Connection button.
- Ensure the server supports the algorithms you’ve selected.
- If the connection fails, check your server documentation or try adjusting the cipher list.
- It’s always recommended to test in a development environment before applying to production.
 Understanding SSH Key-Exchange Algorithms
Understanding SSH Key-Exchange Algorithms
Secure Shell (SSH) relies on key-exchange (KEX) algorithms to establish a shared secret between client and server before encrypting communication.
This process ensures that all data exchanged remains confidential, even if someone intercepts the connection.
There are two main types of key-exchange methods used today:
- Diffie-Hellman (DH) — traditional, based on modular arithmetic.
- Elliptic-Curve Diffie-Hellman (ECDH) — newer, faster, and more efficient, based on elliptic-curve mathematics.
For a full introduction to how Diffie-Hellman works in SSH, see
![]() Baeldung – Enable Diffie-Hellman Key Exchange in Linux
Baeldung – Enable Diffie-Hellman Key Exchange in Linux
 Diffie-Hellman (DH) Algorithms
Diffie-Hellman (DH) Algorithms
These are the classical methods for secure key exchange. Each variant defines a specific key length (“group”) and a hash function to verify integrity.
Technical definitions can be found in the IETF specification ![]() RFC 9142 – SSH KEX Method Updates.
RFC 9142 – SSH KEX Method Updates.
diffie-hellman-group-exchange-sha256
- Uses variable (negotiated) group sizes.
- Employs SHA-256 hashing.
- Provides flexibility and modern security.
 RFC 4419 – Diffie-Hellman Group Exchange for SSH
RFC 4419 – Diffie-Hellman Group Exchange for SSH
diffie-hellman-group16-sha512
- Fixed 4096-bit modulus (Group 16) with SHA-512.
- Very strong encryption, though slower in performance.
 SocketTools – Supported SSH Algorithms
SocketTools – Supported SSH Algorithms
diffie-hellman-group15-sha512
- 3072-bit modulus (Group 15) using SHA-512.
- High security with slightly better efficiency than group16.
diffie-hellman-group14-sha256
- 2048-bit modulus and SHA-256 hash.
- Balanced choice between speed and strength.
 Recommended for general compatibility and compliance with modern standards.
Recommended for general compatibility and compliance with modern standards.
diffie-hellman-group-exchange-sha1
- Older version using SHA-1, now considered insecure.
 RFC 4419 Section 4 – Obsolete Methods
RFC 4419 Section 4 – Obsolete Methods
diffie-hellman-group14-sha1
- Fixed 2048-bit modulus with SHA-1.
- Deprecated due to SHA-1 vulnerabilities.
diffie-hellman-group1-sha1
- 1024-bit modulus and SHA-1 hash.
 Obsolete and disabled by default on modern systems.
Obsolete and disabled by default on modern systems.
 Ezeelogin – SSH KEX and Host Key Algorithms
Ezeelogin – SSH KEX and Host Key Algorithms
 Elliptic-Curve Diffie-Hellman (ECDH) Algorithms
Elliptic-Curve Diffie-Hellman (ECDH) Algorithms
ECDH algorithms achieve the same goal (secure key exchange) but rely on elliptic-curve cryptography, offering stronger security with smaller keys and better performance.
See ![]() Wikipedia – Elliptic-curve Diffie–Hellman (ECDH)
Wikipedia – Elliptic-curve Diffie–Hellman (ECDH)
ecdh-sha2-nistp256
- Uses the NIST P-256 curve with SHA-256.
- Delivers strong 128-bit equivalent security.
- Widely supported in modern SSH implementations.
ecdh-sha2-nistp384
- Based on P-384 curve with SHA-384.
- Offers roughly 192-bit security; used in high-assurance systems.
ecdh-sha2-nistp521
- Uses P-521 curve with SHA-512.
- Very strong, designed for top-tier security requirements.
 RFC 5656 – ECDH Key Exchange for SSH
RFC 5656 – ECDH Key Exchange for SSH
 Comparison Table
Comparison Table
| Algorithm | Type | Key Size | Hash | Performance | Security | Status |
|---|---|---|---|---|---|---|
| diffie-hellman-group1-sha1 | DH | 1024-bit | SHA-1 | Fast | Weak | |
| diffie-hellman-group14-sha1 | DH | 2048-bit | SHA-1 | Medium | Moderate | |
| diffie-hellman-group14-sha256 | DH | 2048-bit | SHA-256 | Medium | Strong | |
| diffie-hellman-group15-sha512 | DH | 3072-bit | SHA-512 | Slow | Very Strong | |
| diffie-hellman-group16-sha512 | DH | 4096-bit | SHA-512 | Slowest | Very Strong | |
| ecdh-sha2-nistp256 | ECDH | 256-bit curve | SHA-256 | Fast | Strong | |
| ecdh-sha2-nistp384 | ECDH | 384-bit curve | SHA-384 | Moderate | Very Strong | |
| ecdh-sha2-nistp521 | ECDH | 521-bit curve | SHA-512 | Moderate | Extremely Strong |
 Best Practice Recommendations
Best Practice Recommendations
- Prefer ECDH algorithms (
ecdh-sha2-nistp256,nistp384,nistp521) for modern systems. - Use group14-sha256 or higher if ECDH is not supported.
- Avoid all SHA-1–based algorithms — they are considered insecure.
- For environments needing maximum compatibility, group14-sha256 is the safest fallback.
![]() Further Reading
Further Reading
- RFC 9142 – SSH Key Exchange Method Updates (IETF)
- RFC 4419 – Diffie-Hellman Group Exchange for SSH
- RFC 5656 – Elliptic Curve Key Exchange for SSH
- Baeldung – Enable Diffie-Hellman in Linux SSH
- Wikipedia – Elliptic-curve Diffie–Hellman
- Ezeelogin – SSH KEX Algorithms Overview
Conclusion
Using the ZappySys Secure FTP Task, you can fully customize SFTP cipher algorithms to match your server’s security requirements. This ensures compatibility and enhances data protection for secure file transfers. With flexible configuration options and an intuitive interface, ZappySys simplifies secure connectivity in SSIS.
Visit our official page to explore more SSIS components, automation features, and real-time data integration tools included in ZappySys SSIS PowerPack.
References
Contact us
If you encounter any issues or have specific questions, reach out to our support team via live chat or support ticket using our email support@zappysys.com.